Analyze with AI
Get AI-powered insights from this Mad Devs article:
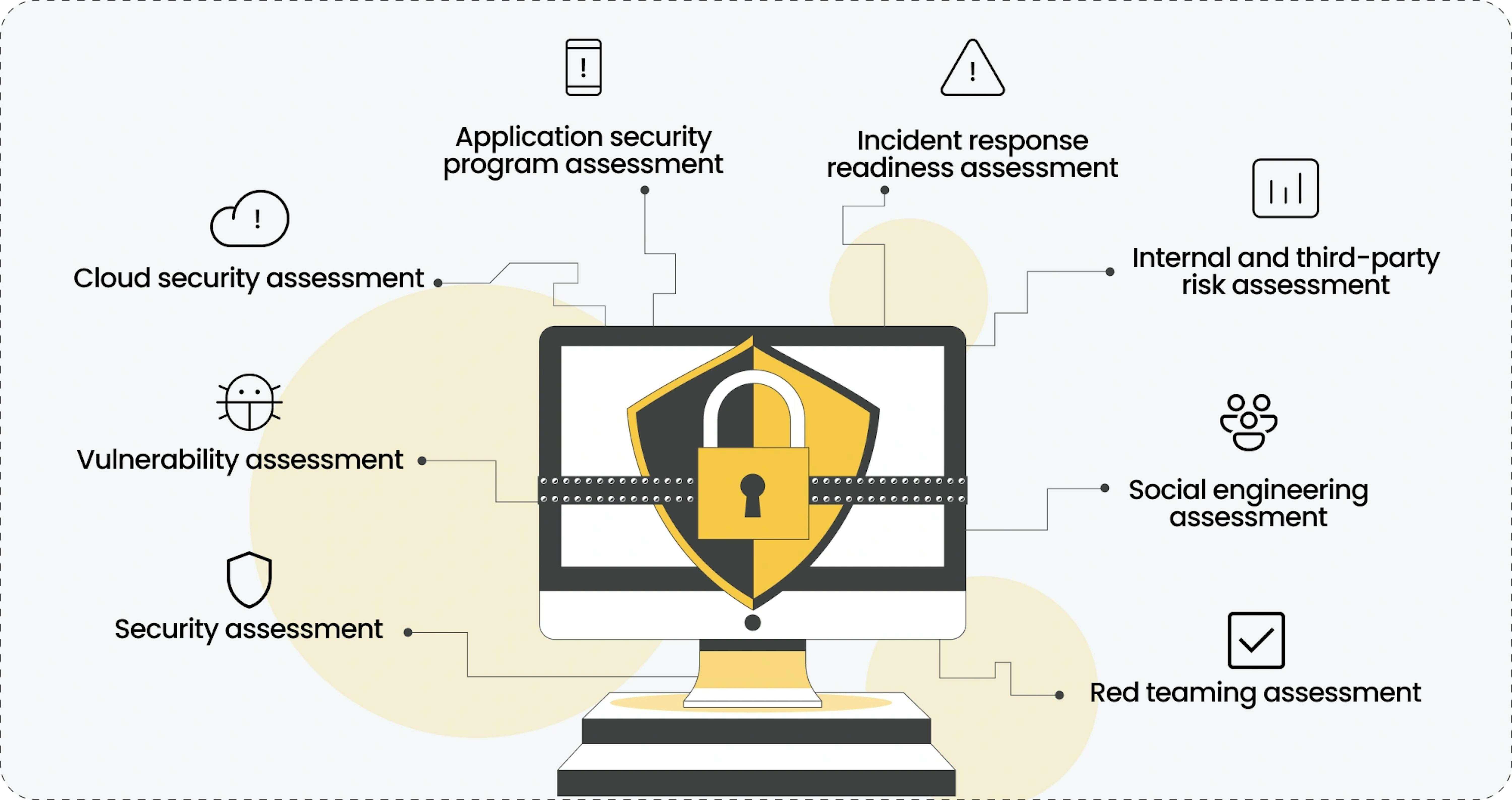
The digital space is getting bigger, providing new opportunities and challenges daily. New ways to disrupt the security of companies are emerging, and in response, new ways of securing it and the types of security assessments are also evolving.
Today, we will look at the main types of security assessments for organizations, their purposes, benefits, and limitations. Also, we will help you understand which type of them will suit better for your company better regarding its domain and specifications. Let's dive into it.
What are the types of cybersecurity risk assessments
Talking more about specific types of security assessments, it is worth noting that security is an initially broad and constantly evolving discipline. Each aspect may undergo an individual review, possibly qualifying as a distinct assessment form. Therefore, let's explore the commonly acknowledged ones.
Security assessment
Covers a broad security review and provides an in-depth analysis of an organization's information systems, policies, and processes.
The main purpose of a security assessment is to verify the overall compliance of information systems with regulations and security standards. This includes reviewing policies and processes, comparing them to security standards requirements, and ensuring compliance with rules and regulations in general.
⚙️ Technologies
Various security auditing tools, including security policy analysis and system troubleshooting, security monitoring system analysis, and configuration analyzers. Automation tools are also used to collect and analyze security performance data.
➕ Benefits
This ensures that the organization's overall security is improved at a fundamental level. This is important for complying with regulations and standards, reducing the risk of security breaches, and increasing the trust of customers and partners.
➖ Limitations
The security assessment process can be resource-intensive for systems to allow for a full audit to take place. There is also a need for highly skilled professionals to interpret assessment results and develop recommendations for security improvements.
Vulnerability assessment
This type of assessment aims to identify security weaknesses and then make recommendations to eliminate possible threats.
The primary goal is to detect and assess potential vulnerabilities before attackers can exploit them. This includes checking system configurations and looking for outdated software components.
⚙️ Technologies
Scanning tools that actively analyze networks, systems, and applications for known vulnerabilities.
➕ Benefits
It provides the ability to take proactive steps to eliminate potential entry points for attacks, ultimately reducing the risk of vulnerability exploitation and increasing the overall level of security.
➖ Limitations
It requires regular updates as new vulnerabilities emerge. Coordinated action plans may also be needed to address discovered vulnerabilities, which may require additional time and resources.
Cloud security assessment
A cloud security assessment is a detailed examination of the security features and controls implemented in an organization's cloud computing environment.
This is aimed at ensuring the security of data stored and processed in the cloud, as well as verifying that the cloud provider's security controls comply with industry standards.
⚙️ Technologies
Cloud resource configuration assessment tools, cloud security monitoring systems, and tools to analyze protocols and data encryption.
➕ Benefits
It assures that an organization's cloud infrastructure is under the proper level of protection. This promotes compliance with industry standards and customer confidence in the security of personal data.
➖ Limitations
Dependence on cloud service providers creates limitations in controlling the entire infrastructure. Organizations may face limitations in configuring the security provided by the cloud provider, which requires careful planning and alignment of security measures.
Application security program assessment
It comprehensively examines an organization's overall policy for securing its software applications.
The primary goal is to ensure that software applications are secure at all stages of their lifecycle, including the development, testing, and support processes, to ensure that all phases meet high-security standards.
⚙️ Technologies
Static and dynamic code analysis tools and code review systems are used to perform application security program assessments. As well as integrating security analysis tools into the development process and verifying their effectiveness.
➕ Benefits
It reduces the risk of vulnerabilities and data leaks in applications, seamlessly publishing applications to stores, and increasing user confidence.
➖ Limitations
Such integration into the development process can cause resistance from the development team. In addition, regular process updates are required to keep up with changes in the technology stack and security requirements.
Incident response readiness assessment
An incident response readiness assessment tests and evaluates an organization's ability to respond to information security events.
The main purpose is to assess the effectiveness and responsiveness of the means to respond to potential security breaches. This includes assessing the strategies, processes, and resources designed to prevent, detect, and quickly remediate incidents.
⚙️ Technologies
Real-time incident testing tools, automation tools for anomaly detection, and incident management systems are used to conduct incident response readiness assessments.
➕ Benefits
It provides the business with confidence that the organization can respond effectively to security breaches, minimize potential losses, and recover quickly from an incident.
➖ Limitations
The assessment requires regular updates to reflect the organization's infrastructure and technology stack changes. Also, a lack of coordination and alignment between different levels of the organization can reduce the effectiveness of response plans.
Internal and third-party risk assessment
It's a systematic process for identifying and analyzing potential threats to an organization's assets, including both internal and third-party threats.
The objective of the risk assessment is to prioritize the implementation of security measures to address both internal and third-party threats. This includes assessing the likelihood of security breaches by third parties, such as service providers and external interactions.
⚙️ Technologies
Methodologies like qualitative and quantitative analysis, and technologies including risk modeling software, threat analysis tools, and third-party risk management systems.
➕ Benefits
It helps identify potential threats and weaknesses within an organization and determines the likelihood of events that can damage business processes and information resources. Also, it allows you to create more flexible security policies, diversify risks, and allocate resources to minimize potential losses.
➖ Limitations
Subjectivity in assessing internal and third-party risks can arise from limited control over vendors' security practices. Additionally, it requires constant updating, especially in the context of changes in third-party relationships and updates to their security infrastructure.
This one is more than a tech review and evaluates an organization's defenses against attempts to manipulate or trick employees into obtaining confidential information or unauthorized access.
The main purpose is to assess employee awareness and resilience to social engineering attacks.
⚙️ Technologies
It utilizes tools to simulate real-world social engineering attacks, tactics to validate training effectiveness, and employee vulnerability testing procedures.
➕ Benefits
As the weakest factor in security remains the human being, it can fail the most advanced system. Therefore, by increasing employee awareness and reducing exposure to social engineering attacks, you can provide an additional layer of protection against sensitive information leakage and safeguard corporate resources.
➖ Limitations
Its effectiveness can be limited if employees are aware of the testing. In addition, results may be skewed due to differences in real-world scenarios and test simulations.
Red teaming assessment
This represents a comprehensive and multifaceted approach to testing and assessing the strength of an organization's defenses. In this type of assessment, the red team simulates the actions of real attackers to identify weaknesses in systems, processes, and people.
The main goal here is to provide realistic testing of an organization's security systems, proactively identify vulnerabilities that attackers could exploit, and assess the effectiveness of defenses against real threats.
⚙️ Technologies
Different tools and frameworks, including network and application security testing, social engineering, physical intrusions, and specialized automated tools to simulate attacks.
➕ Benefits
It gives an organization a unique perspective on identifying security weaknesses that might have gone undetected in traditional assessments. It helps improve defense strategies and prepares personnel for threats closest to the real thing.
➖ Limitations
Red Teaming requires significant resources and can be costly. In addition, the results can cause anxiety among staff, so communication and expectations need to be carefully managed.
🛡 If you think you need absolutely every one of them, but it's too long, expensive, and complicated that it's easier to leave it as it is, find out otherwise by checking out our Enhancing the GuardRails solution case study.
How to choose a cyber security risk assessment for your organization
Choosing a specific type of cybersecurity assessment is very individual and depends on your organization's particular needs, goals, and features. Let's look at the main questions and points to consider.
| ASSESSMENT TYPE | CRITICAL QUESTIONS | CRITICAL POINTS |
|---|---|---|
| Security assessment | a. Which information assets in your organization are considered most valuable and critical to business processes? b. Which security regulations and standards most apply to your industry, and how confident are you that they are being met? | Organizations operating in regulated industries or processing sensitive customer data, such as financial institutions, healthcare providers, and government organizations. |
| Vulnerability assessment | a. What types of data and applications are most valuable to your organization, and how are they at risk? b. How often do you update and adapt your systems to minimize the risk of new vulnerabilities? | Companies that actively use online space and process critical data, especially in e-commerce, financial, and healthcare sectors. |
| Cloud security assessment | a. What types of data do you store and process in the cloud, and what are the security requirements for that data? b. How do you manage access to cloud resources, and do you prepared to assess your cloud provider's compliance with security standards? | Companies provide active implementation or use of cloud technology for data storage. This is especially relevant for those who work with big data from multiple customers, such as retailers and cloud service companies. |
| Application security program assessment | a. Which phases of the application lifecycle pose the greatest security risk, and are you prepared to assess their effectiveness? b. How are security tools integrated into the development process, and what challenges do you see in implementing them? | Software product developers and companies that actively interact with customers through applications. |
| Internal and third-party risk assessment | a. Which critical business processes depend on internal and third-party vendors, and what risks does this create? b. How do you assess the reliability and security of third-party vendors, and are you prepared to assess their impact on your security? | Large companies with an extensive business structure and a high degree of dependence on third-party partners, especially in the financial, transportation, and industrial sectors. |
| Social engineering assessment | a. What types of social engineering pose the greatest risk to your organization, and how can they be used to gain unauthorized access? b. What areas in employee behavior could potentially be weaknesses in preventing social engineering? | Organizations where employees have access to sensitive data or physical infrastructures such as financial institutions, healthcare facilities, or government institutions. |
| Incident response readiness assessment | a. What incidents pose the greatest threat to your organization, how are you prepared to handle them? b. How often do you update and test your incident response strategies, and are you prepared to make regular improvements? | Companies where rapid incident detection and response are critical will find this type of assessment is essential to business continuity, especially in the financial, medical, and government defense sectors. |
| Red teaming assessment | a. What specific threats and attack scenarios are most realistic for your organization? b. Are you prepared to test your defenses using multiple methods, including simulations of real attackers? | Organizations are at high risk of targeted attacks, as are large enterprises with high stakes in security, especially in defense, financial, and energy infrastructure. |
Questions from the list seem fundamental to you, and their answers will help you understand which type of assessment will most likely be helpful for your business.
Summary
Today, most businesses have an online presence, and some are exclusively online. This makes the digital space, and all the physical infrastructure that supports it, a limitless space of opportunity for attackers.
However, you now know about the main types of security assessments organizations do, what aspects of security they seek to improve, what benefits they bring to the business, and what limitations they have.
Also, you now know the main questions and critical considerations that will help you choose the type of security assessment most appropriate for your company.
For more details or personalized assistance, you are always welcome to contact our experts for a free consultation. We will help you choose the most suitable and effective assessment, keeping your business operations uninterrupted and ensuring safety-critical to your organization.










Social engineering assessment