Analyze with AI
Get AI-powered insights from this Mad Devs article:
Today, cloud services have become an integral part of the business infrastructure for most companies, providing flexibility, scalability, and accessibility. However, as cloud computing continues to evolve, new opportunities arise. In a multi-cloud environment, organizations use two or more cloud providers for various purposes to achieve optimal efficiency and precision in business operations, which we will detail below.
Nevertheless, increased complexity presents various specific challenges and security threats that require special attention and corresponding security strategies. These strategies go beyond standard cloud security solutions and encompass their extension and deepening.
Therefore, we will comprehensively explore multi-cloud security, including the key challenges and threats organizations face in such environments. Additionally, we will present essential practices and recommendations that help organizations mitigate threats and ensure the security of their multi-cloud environments. Furthermore, we will highlight the necessity of security automation and the application of DevSecOps principles. And much more. So join this highly informative read.
What is cloud security?
Cloud security is a compilation of strategies and measures designed to safeguard data, applications, and infrastructure within a cloud environment. While cloud service providers offer businesses the opportunity to rid themselves of the expenses associated with establishing and maintaining their own computing infrastructure by providing access to ready-made resources and services, the efficiency and security of these services rely on the client companies.
Key cloud security practices
Cloud security encompasses an array of proven practices; let's remember the key ones.
Areas of responsibility in cloud security
Depending on the cloud service model, the responsibility for various security aspects is distributed differently between the provider and the client.
- In Infrastructure as a Service (IaaS), the cloud provider supplies the fundamental infrastructure (servers, network, storage), while the client is responsible for the security of operating systems, applications, and data they deploy in the cloud.
- In Platform as a Service (PaaS), the provider offers not only the infrastructure but also a development platform, including operating systems and development tools. The client is responsible for the security of the applications they develop and the data these applications process.
- In Software as a Service (SaaS), the provider delivers ready-to-use applications and is responsible for their security. However, the client still holds responsibility for their configuration and the security of the data they store and process in these applications and for managing access to this data.
📖 Maximize your SaaS potential: Discover how the right pricing strategy can drive growth and increase market share
Data management
This encompasses cryptography and key management. Cryptography is used to protect data during its storage (at rest), transmission (in motion), and utilization (in use). Key management ensures cryptographic keys' secure storage, generation, exchange, and usage.
Access management
This involves authentication and authorization. Authentication verifies the identity of a user or system attempting to gain access. Authorization determines what actions are permitted for the authenticated user or system.
Compliance with security standards
Various security standards may be applicable in the context of cloud security. These can be general standards such as ISO 27001 or industry-specific ones like PCI DSS for the payment industry or HIPAA for healthcare. Adhering to these standards helps to ensure security and compliance with regulatory requirements.
By the way, we have an in-depth article on HIPAA Compliance on Cloud Infrastructure. There we detail what HIPAA is, how our engineers technically ensured compliance, and the challenges they faced along the way. We highly recommend reading.
What is a multi-cloud strategy?
The cloud industry is evolving, and many cloud providers have emerged, each offering unique services and conditions. This has given rise to the multi-cloud strategy, in which more than 76% of companies are already using two or more cloud providers, and this trend continues to grow.
A multi-cloud strategy is an approach where a company utilizes a combination of public, private, and hybrid clouds. It allows them to leverage cloud providers' best features and services for specific business operations and comply with the regulations. For instance, one provider may offer high-performance computing resources, while another may provide advanced analytical tools or more favorable data storage conditions, and in addition, some regulations require that citizen data be kept within certain geographical borders.
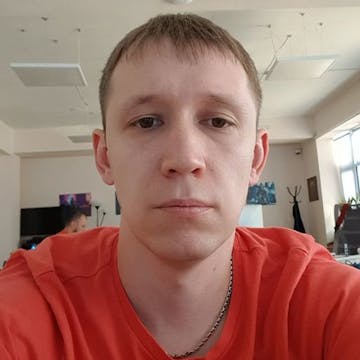
Multi-cloud strategy benefits
Transitioning to a multi-cloud strategy offers a range of benefits that can help organizations improve their operations, increase efficiency, and ensure the reliability of their systems. Let's take a closer look.
- Specialization
Allows organizations to optimize their infrastructure for specific workloads using specialized services from different cloud providers. For example, an organization might use a cloud service that offers high bandwidth for processing large volumes of data, while another service might be used for applications requiring high reliability and availability. This allows organizations to maximize the advantages of each cloud provider, considering the specific requirements of their workloads. - Cost efficiency
Enables organizations to optimize their costs. Different cloud providers may offer varying rates and conditions for their services. Organizations can choose among these providers depending on their current needs and budget. This might include using cheaper services for less critical workloads or employing more expensive but reliable services for mission-critical applications. By the way, we have a set of articles in which we share how to optimize infrastructure and development costs based on our first-hand experience. - Disaster recovery
It enhances the reliability and availability of the organization's systems. If one cloud provider encounters issues, another provider can continue to serve. This reduces the risk of downtime and ensures business continuity. Moreover, a multi-cloud strategy allows organizations to recover from disasters more quickly, as data and applications can be distributed across different cloud platforms. - Avoidance of vendor lock-in
By utilizing multiple cloud providers, organizations can avoid being overly dependent on a single provider. This provides more flexibility in negotiating contracts and scaling resources and ensures that the organization is not at the mercy of a single provider's pricing changes or service alterations. - Improved security and compliance
Using multiple clouds can provide a layer of security as the data is spread across different environments. Also, some cloud providers might offer better security features or compliance with particular standards crucial for specific business parts. - Geographical presence
It provides better global coverage and services closer to end-users. Different providers might have data centers in various locations, which can be leveraged for faster response times and compliance with regional data laws. - Innovation and access to the latest features
Different cloud providers often roll out new features and technologies. By having a multi-cloud strategy, organizations can quickly adopt and experiment with these innovations without being tied to the offerings of a single provider.
In conclusion, a multi-cloud strategy offers organizations greater flexibility, cost efficiencies, reliability, and access to specialized services that can help drive business goals and maintain robust and resilient operations. However, it is essential for organizations to carefully manage and orchestrate their multi-cloud environments to avoid complexity and ensure that they can fully realize the opportunities.
What is multi-cloud security?
Multi-cloud security refers to measures employed to safeguard data, applications, and infrastructure distributed across multiple cloud platforms. Within a multi-cloud environment, data and applications can migrate between different cloud platforms, each with its own security standards and control mechanisms. This introduces complexity in security management as it is essential to consider these variances and ensure protection across all layers and components.
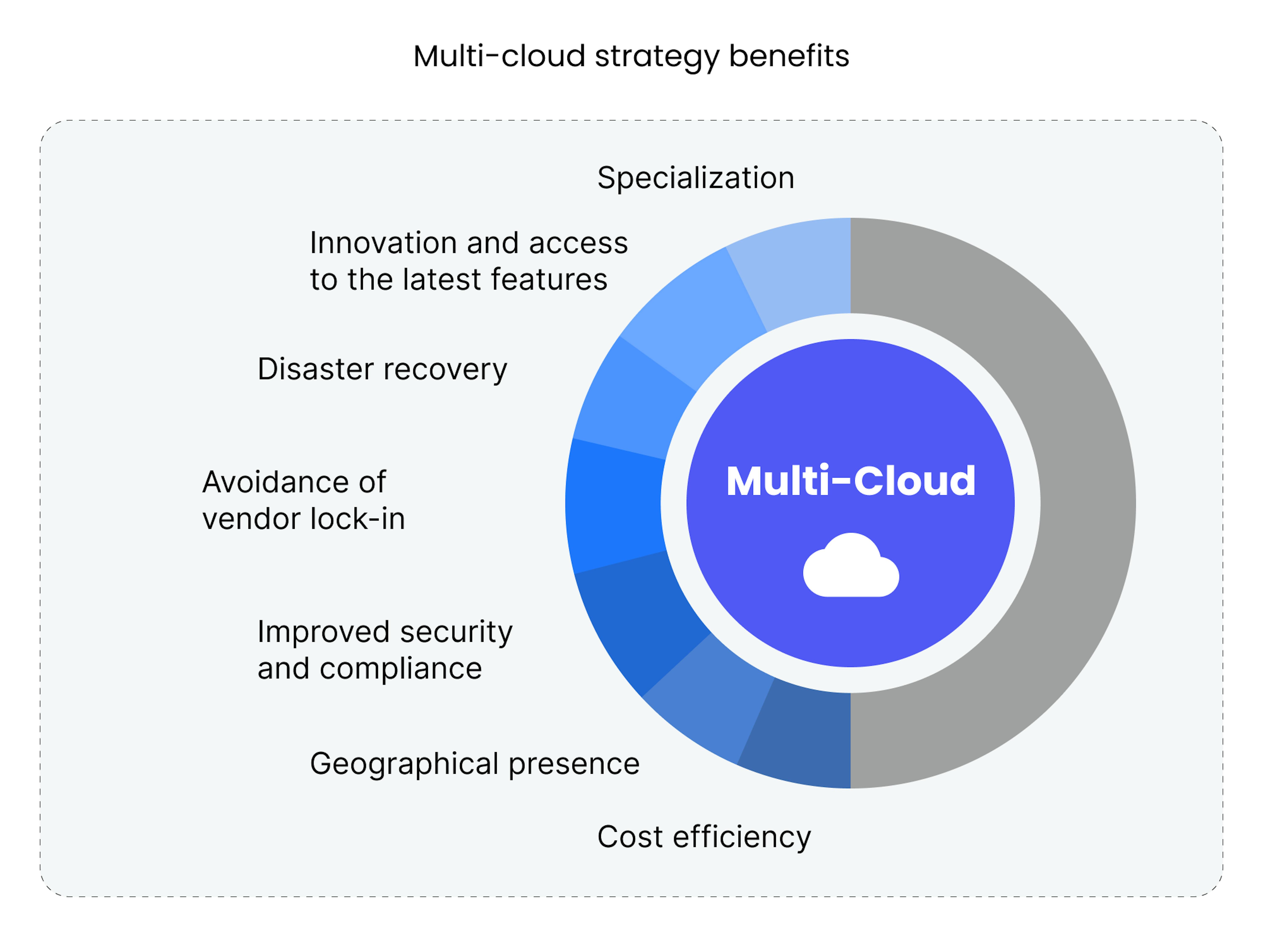
Multi-cloud security challenges
Along with these advantages, multi-cloud environments present a series of unique challenges.
Staff training
Staff working with multi-cloud environments must be familiar with general cloud security principles and the specific features of each cloud platform. This may entail training in handling specific security tools and interfaces and understanding each cloud provider's distinct security policies. Comprehensive training for staff in these areas may require significant time and financial investment.
Cloud migration management
Migration of data and applications between different cloud platforms demands meticulous planning and execution. It involves ensuring the security of data during transmission, as well as managing access to the data on the new platform. This process can be complex and requires substantial effort to guarantee its completion.
Security policy management
In a multi-cloud environment, ensuring consistent security policies can be challenging. Each cloud provider may have its own tools and procedures for security management, which may vary from other platforms. This may create complexities in maintaining consistency and effectiveness in security policies.
Access and identity management
Managing access and identity within a multi-cloud environment can be intricate due to differences in identification and authorization systems among various cloud providers. This may necessitate sophisticated Identity Management Systems or Cloud Access Security Brokers.
Encryption management
In a multi-cloud environment, managing encryption keys can be a complex task. Keys need to be accessible across all relevant cloud platforms while ensuring their secure storage and usage. This may call for specialized encryption key management solutions that support multi-cloud environments.
Resource management
Managing resources in a multi-cloud environment can be challenging due to differences in pricing structures and reporting mechanisms among cloud providers. This may necessitate specialized tools for monitoring resource utilization and optimizing costs.
Monitoring challenges
Monitoring activity and security events in a multi-cloud environment can be challenging due to differences in logs and audit data provided by various cloud platforms. This may require centralized security monitoring systems capable of aggregating and analyzing data from different sources.
Multi-cloud security threats
Multi-cloud solutions can also come with unique security threats. These threats can arise due to various factors, including configuration complexity, non-compliance with regulatory requirements, access and identity management vulnerabilities, and threats across different layers, including networks, applications, and APIs.
Configuration non-compliance and access management
Each cloud provider has its own tools and methods for security configuration and access management in a multi-cloud environment. This may encompass different authentication methods, such as multi-factor authentication (MFA) or single sign-on (SSO), varied network access settings, such as access control lists (ACLs) or security groups, and distinct access management policies, like role-based access control (RBAC) or attribute-based access control (ABAC). These variations must be considered when configuring security to avoid configuration non-compliance, increasing the risk of unauthorized access to sensitive data. It can also result in weak or incompatible access policies, heightening the likelihood of internal and external security threats.
Non-compliance with regulatory requirements
Each cloud provider has its own procedures for ensuring compliance with various regulatory requirements, such as GDPR, HIPAA, or PCI DSS. This can encompass different data encryption methods, distinct access management policies, and various auditing methods. Not considering these differences when processing or storing data can lead to non-compliance with regulatory requirements and potential penalties.
Multi-layer threats
In a multi-cloud environment, plenty of threats exist at different layers, including networks, APIs, and applications. At the network layer, this might involve misconfiguration of network devices, such as firewalls and load balancers, which can lead to distributed denial-of-service (DDoS) attacks or data interception. At the application levels, threats can include vulnerabilities in application code, allowing SQL injections or cross-site scripting attacks, as well as vulnerabilities in APIs, which can allow attackers to bypass access controls or manipulate API functionality through injection attacks or brute force attacks based on credential stuffing.
Encryption threats
Encryption is a primary method for protecting data in the cloud, but it also presents unique threats. If encryption keys are lost or compromised, this can lead to losing access to data or data exposure. This could occur due to an external attack, internal misuse, or a simple error. Some cloud providers may also use their key management systems, which might not be compatible with other systems.
Insider risk
In a multi-cloud environment, the risk of insiders increases as more individuals access cloud resources. Employees, contractors, business partners, and even malicious actors can gain access to systems through weak or compromised accounts. This could lead to information leakage, the introduction of malware, or even sabotage of the cloud infrastructure.
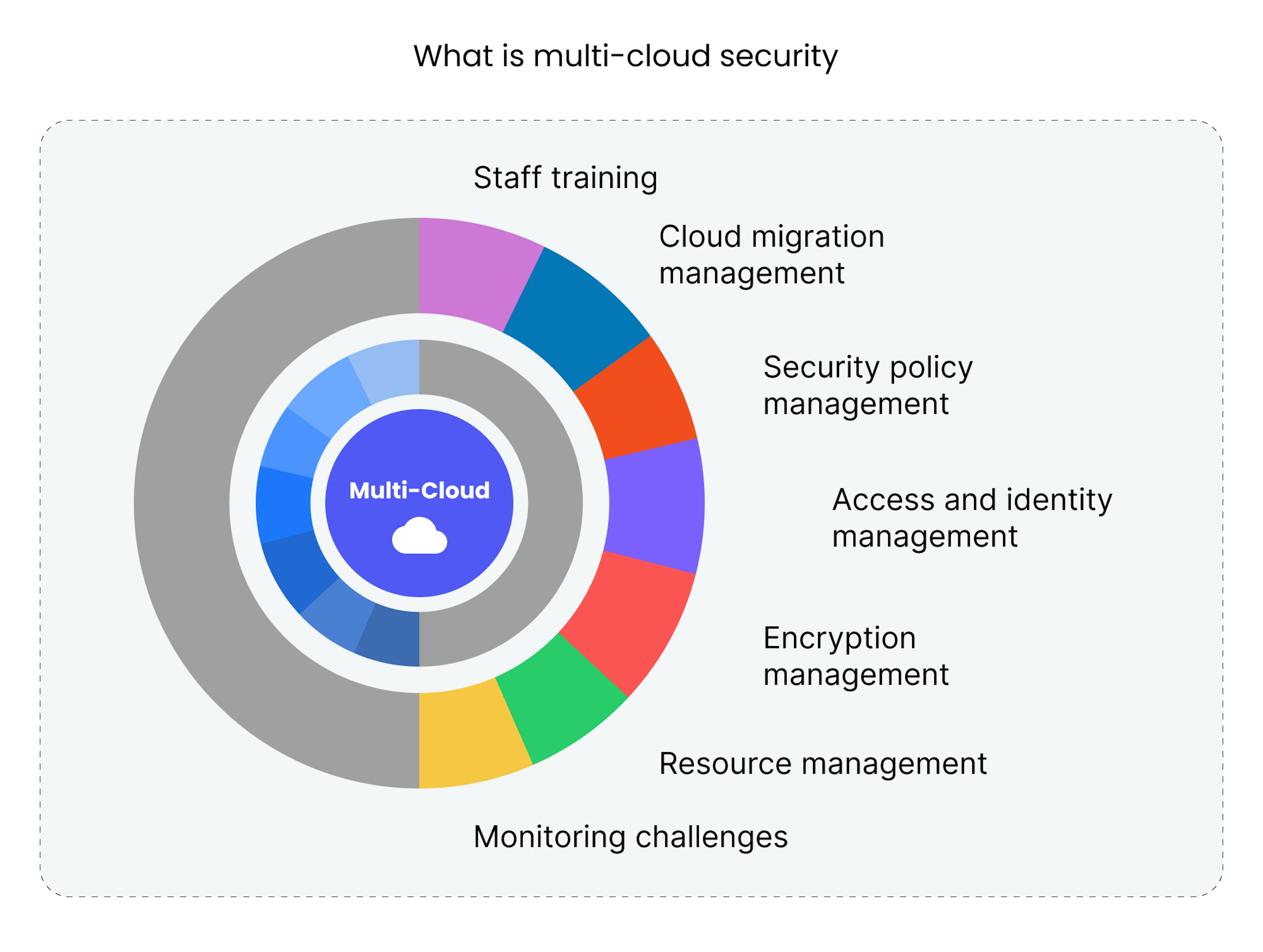
12 best practices for multi-cloud security
In a world where multi-cloud environments are becoming increasingly common, the security of these environments is a top priority. Here are some best practices that will help secure your multi-cloud environments.
Team education. Ensure that your team deeply understands multi-cloud security principles, including the specifics of working with different cloud platforms and security protocols.
Incident response plan. Develop detailed incident response plans that consider each cloud environment's specifics, including procedures for detecting, isolating, and mitigating incidents.
Responsibility allocation. Clearly define the boundaries of security responsibility between your company and cloud providers, considering the type of service provisions such as IaaS, PaaS, and SaaS, as well as the specifics of SLA contracts and the features of SLO and SLI.
Unification of security tools. Standardize security tools and their usage protocols to ensure consistency and the ability to respond quickly to incidents in any cloud environment.
Consistent security policies. Develop and implement unified security policies that will be applied across all cloud platforms, thereby ensuring a homogeneous level of protection.
Security first. Integrate security principles from the beginning of development and deployment processes, and the prior criteria for choosing cloud providers.
Identity and access management (IAM). Develop IAM strategies that ensure role-based access control and the least privilege principle to prevent unauthorized access to cloud resources.
Data encryption. Apply encryption methods at all data lifecycle stages — during storage, transmission, and processing — to ensure their confidentiality and integrity.
Encryption key management. Implement encryption key management strategies that take into account regulatory requirements and the need to ensure access to data when necessary.
Ensuring protection across cloud platforms. Use security tools, such as CloudGuard from Check Point, that can provide continuous protection of data and applications as they migrate between different cloud platforms.
Ensuring visibility in a multi-cloud environment. Use monitoring and analytics tools, such as Splunk or Datadog, to provide full visibility and control over all your cloud environments, allowing for timely detection and response to security incidents.
Regular security testing. Conduct regular security audits and penetration tests to detect and mitigate vulnerabilities on time and verify the effectiveness of your security measures. This may include using tools such as OWASP ZAP for penetration testing or services from other companies to conduct security audits.
Why is automation essential for cloud security?
Given the complexity of multi-cloud environments and the many components that need to be managed, automation plays a key role in ensuring security. Automation helps ensure continuous compliance with security policies, reduces the likelihood of human errors, and speeds up the response to security incidents. This can include automatic detection of and response to anomalies in the cloud environment, automated access management, and automatic updates of security configurations.
Why is DevSecOps essential for cloud security?
In a multi-cloud environment, where system complexity is increased, ensuring security from the earliest stages becomes critically important. DevSecOps, or integrating security into development and operations processes, ensures security at all application lifecycle stages, starting with architectural design. This can include using automated tools for code vulnerability scanning, integrating security policies into CI/CD processes, and regular security testing during development and operations.
Finding and using the right cloud security solutions
Each company has unique needs and capabilities, so selecting cloud security solutions that best match your requirements is important. Here are the general steps for choosing and using the right cloud security solutions.

- Understanding your requirements
Identify your key security requirements, including the level of protection required for your data and applications, regulatory compliance, and the specifics of your cloud infrastructure. - Assessing available solutions
Research the market and evaluate available cloud security solutions, considering their functionality, compatibility with your cloud environment, and cost. - Comparing and evaluating solutions
Compare the chosen solutions by evaluating them on key parameters such as the level of protection, flexibility, scalability, and cost. - Conducting a proof of concept
Carry out a proof of concept with the selected solutions to verify their effectiveness and compatibility with your cloud environment under real-world conditions. - Implementing the chosen solution
After selecting an appropriate solution, implement it, ensuring its integration with your cloud environment and existing security processes. - Monitoring and adjusting
After implementing the solution, continuously monitor and adjust its settings and parameters following changing conditions and security requirements. - Regular review and updating
Conduct regular reviews and updates of your cloud security solution to ensure its relevance and effectiveness in the face of constantly changing threats and security requirements.
Summary
Now you know well the advantages multi-cloud offers compared to a single-cloud strategy, such as the ability to leverage the best features of each cloud provider for more precise and effective business operations. However, this also places greater responsibility on security, as multi-cloud security introduces a broader range of attack vectors and potential for mistakes. By gaining a deeper understanding of these challenges and how to address them, you can approach the migration or optimization of your diverse infrastructure with increased responsibility and effectiveness.
Also, our experts are available for a free consultation if you need assistance optimizing or automating your cloud operations. And they will provide you with all the knowledge and experience necessary for successful completion.